Terrier is an intelligent packet sniffing and analyzation tool that helps in consolidation of data, extract valuable insights and enable analytics for tracking and identifying suspects to help ease the investigation process.
Brief
Exploring the Proactive Role of Advanced Communication Analytics in Crime Prevention.
Collaboration
School of Planning and Architecture, Bhopal
+
Cleartrail Technologies, Indore
Methodology
Qualitative Research
Competitor Research
Wireframing
Rapid Prototyping
Duration
18 Weeks
Tools
Category
UX/ UI Design
Information Design
Category
UX/ UI Design
UX/ UI Design
UX/ UI Design
UX/ UI Design
Information Design
Aim
The project aims to design a solution for creating a platform for analyzing and investigating large amounts of data to identify potential criminal suspects using communication analytics.
Problem
The law enforcement and intelligence agencies struggle with analyzing and segregating huge amount of data with untrained staff and no appropriate tools.
Challenges
The complexity of data created cognitive overload for untrained users.
The designs needed to be intuitive yet complex to maintain access to information.
Data visualizations needed familiarity with the users to reduce the time for onboarding and training.
Scope
Target Audience
Law Enforcement Agencies (LEA)
Law Intelligence Agencies (LIA)
Medium
Digital Interface
Using AI and ML for advanced data analysis
Finding anomalies in data for better computing
Macro to micro data segregation
Comparative pattern of life
Intelligent comparing features
Auto suggestions, anomaly and pattern analysis
Auto report creation and sharing options after analysis
Features
Especially designed for LEAs and LIAs to help solving crime
A companion for aiding in investigation rather than an analysis software
Easy to use and understand without training
Only for data packet analysis
USP


Design Process
Secondary Research
Methodology
Online Research
Expert Interviews - Tech and Research Team for Communication Analysis
Competitor Research
Insights
Multiple protocols
Getting the data for investigation requires many protocols amongst the system
Derivation
Data can be derived from various means like NSPs, private companies and public

Collection
Data is recorded and collected through various National and International Organizations.
Analyzation Platforms
Various platforms like Wireshark, WinPcap, TCPDump, Webtrail, etc are used for analyzing raw data files into investigation material
Data Types
There are various typed of files that have different kinds of data eg. PCap, PSTR, log data, alert data, etc
Collaborations
Govt. is collaborating with various private organizations and creating platforms and training for the police.
Primary Research
Methodology
One-on-one interviews with Target Audience:
Law Enforcement Agents (LEA)
Law Intelligence Agents (LIA)
Insights
Varying Qualifications
There is no qualification (education level and age) for people who view and analyze such amount of data.
No Right Tools
On field, Indian police use Pivot chart in excel or Wireshark for data analyzing.
Need for Accuracy
They have a requirement for accurate data rather than user friendly interface
Customization
For customized softwares, semi govt. companies are given tenders to create a software.
Reliability of Tools
Even if the software provides concise data, the process is rechecked manually
Data as Evidence
Data is used as a supporting evidence in an investigation, most work is done on field with physical evidence
Competitor Research
Pros
Elaborate and handy software
Variety and build for general audience eg. Private companies for network analysis and data extraction
Network Top to bottom information
Cons
Elaborate and handy software
Variety and build for general audience eg. Private companies for network analysis and data extraction
Network Top to bottom information
Competitors
PCAP Analysis

Network Monitoring

Design Insights
Be the Guide, not tool
Inclusive
Create a tool that can be used with varied audience, is easy to understand and intuitive.
Go beyond use as a tool but more as a guide/companion in the investigation.
Future Oriented
Use of technology for advanced and intelligent analysis of data to get to meaningful insights.
Visually Appealing
Visual representation of data for better understanding and self analysis.
Persona
Analyst: Type A
Depending on the responsibilities and the level of superiority, three types of personas can be created based on the age, experience, and behaviour associated with each personality type. They are:
Analyst Type A
A young Sub-constable of police with only a year of experience
is in charge of data analysis for a case investigation.
Analyst Type B
A sub-inspector with 20 years of on-field service who is given the responsibility of analyzing data for a case investigation.
Investigator
A deputy director of IB who is investigating a case and requires insights from data obtained at the scene.

User Journey Map
Jagdish’s journey to analyze data
Scenario
Jagdish wants to capture the data files from the network of a target and compare it with the files of other suspects to get plausible connections between them. He wants to give relevant data report to his senior officer in time to help with the investigation.
Expectations
Analyze the information fast
Get desired data with a click of a button
Get print ready reports in time
Options to add personal comments and physical discoveries.
Sharing and collaborating with teams.
Better sharing options
Digital repository of data files.
Hopeful
Excited
Enthusiastic
Excited
Content
Optimistic
Anxious
Stressed
Overwhelmed
Exhausted
Agitated
Annoyed
Going to the targets place and capturing data
Jagdish sits in the same network as the target and captures all the files in that device
Use AI and ML to help with investigations
Highlight any information that can be useful.
Innovative data visualizations to help in better analysis and comparison of information.
Auto analysis to save time.
Coming back and analyzing data that was captured
He comes back to office and puts all the files for analysis.
He gets various parameters of analysis and gets details on the target.
Downloading the report with suggestions and findings
He discovers a few connections between them and puts auto suggestions and his own suggestions into the report.
He takes the printout of the detailed report and takes it to his team and seniors to discuss.
Comparing the data with a previous data file of another target
He is then asked to find any connections to a previous target.
He uploads a data file from previous records and analyzes it to extract information.
He then compares with the captured files based on parameters that were found on field
User Flow

Information Architecture

Wireframes
.png)
.png)
.png)
.png)

.png)

Why Terrier?
Font: Delight Bold
Typography
Terriers are a type of dog species that are exceptionally good at sniffing out narcotics and explosives.
They are friendly and good companions and are used by law enforcement.
Color Scheme
Neutral, Dark, High Contrast, Familiar
Heading
Subheading
Body
Mulish Semi Bold
Mulish Medium
Mulish Regular
#FFD45A
#FFFFFF
#B2B6BC
#2F3638
#1A1E1F
#000000
Visual Design
Identity

Prototype
Signup/ Login


Creating a New Case
The analysis of files can only be done after creating a case. A case will contain all the details regarding the incident. To create a new case, files have to be either captured through network traffic or uploaded from archives. The case files are then processed to view detailed outcomes.



Case Contents
Once the files are processed, various parameters called Case Contents are analyzed to get to the results to the investigation.

There are a total of 12 Case Contents that can be analyzed through Terrier. Namely:
1. Location
2. IP Address
3. VoIP Calls
4. MAC Address
5. Applications
6. Devices
7. Protocols
8. Servers
9. Domains
10. Email ID
11. Phone Number
12. Media (Photos, Videos, etc)

Case Contents Interactions: Location
The case contents can be analyzed by expanding the view, Selecting a timeline, Searching through Terrier AI, Adding personal notes and Marking the results.





Case Contents Interactions: VoIP Calls
VoIP Calls can be further expand and the connections can be highlighted.

Case Contents:
Media Records



Case Contents:
IP Address Records

Pattern of Life
Pattern-of-life analysis is a method of surveillence that documents or understands the habits of a person or population
Here, the pattern of life is like a comparitive analysis of all the case components in a timeline.

A single entity in the timeline can also be viewed.

Pattern of life can be viewed for multiple suspects.

Selected case contents can be compared.

Cross Comparison
A cross-comparison from the previous cases of parameters like Suspects, Cases or Contents can be done, and valuable insights can be brought out to ease the investigation or uncover patterns between cases.


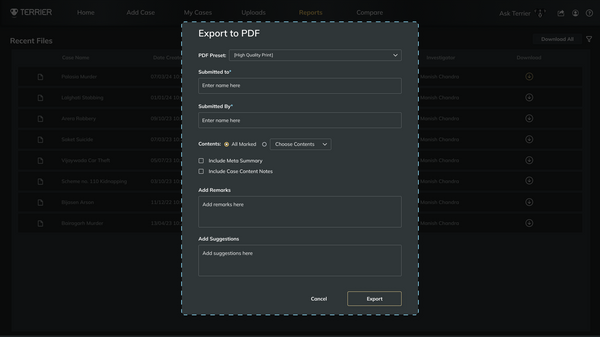
Taking a report
After the analysis, a printed report can be generated to pass the information to a team or a superior officer. The printed report will contain a meta summary, all marked parameters with details and personal notes.